On April 13, 2026, Representatives Josh Gottheimer (D-NJ) and Elise Stefanik (R-NY) introduced H.R. 8250 — the “Parents Decide Act.” The bill’s premise is straightforward: require every operating system provider in the United States to verify the age of every user. If the user is under 18, a parent or legal guardian must be involved.
This isn’t another state-level experiment. It’s a federal bill that, if enacted, would create a single nationwide standard for OS-level age verification — replacing the patchwork of state laws that are already giving compliance teams headaches. And it would fundamentally change the relationship between app developers, OS providers, and age verification infrastructure.
We covered the voluntary shift toward device-level age signals from Apple and Google in March. H.R. 8250 is a different beast entirely. This isn’t Apple choosing to offer a Declared Age Range API. This is Congress potentially mandating that every OS provider build age verification into the device setup flow — and expose that data to app developers via API.
Here’s what the bill says, what it doesn’t say, and what you should be thinking about now.
What H.R. 8250 Actually Requires
The bill’s full text wasn’t publicly available at the time of its introduction, but the title, sponsor statements, and committee referral give us enough to work with. Here’s what we know:
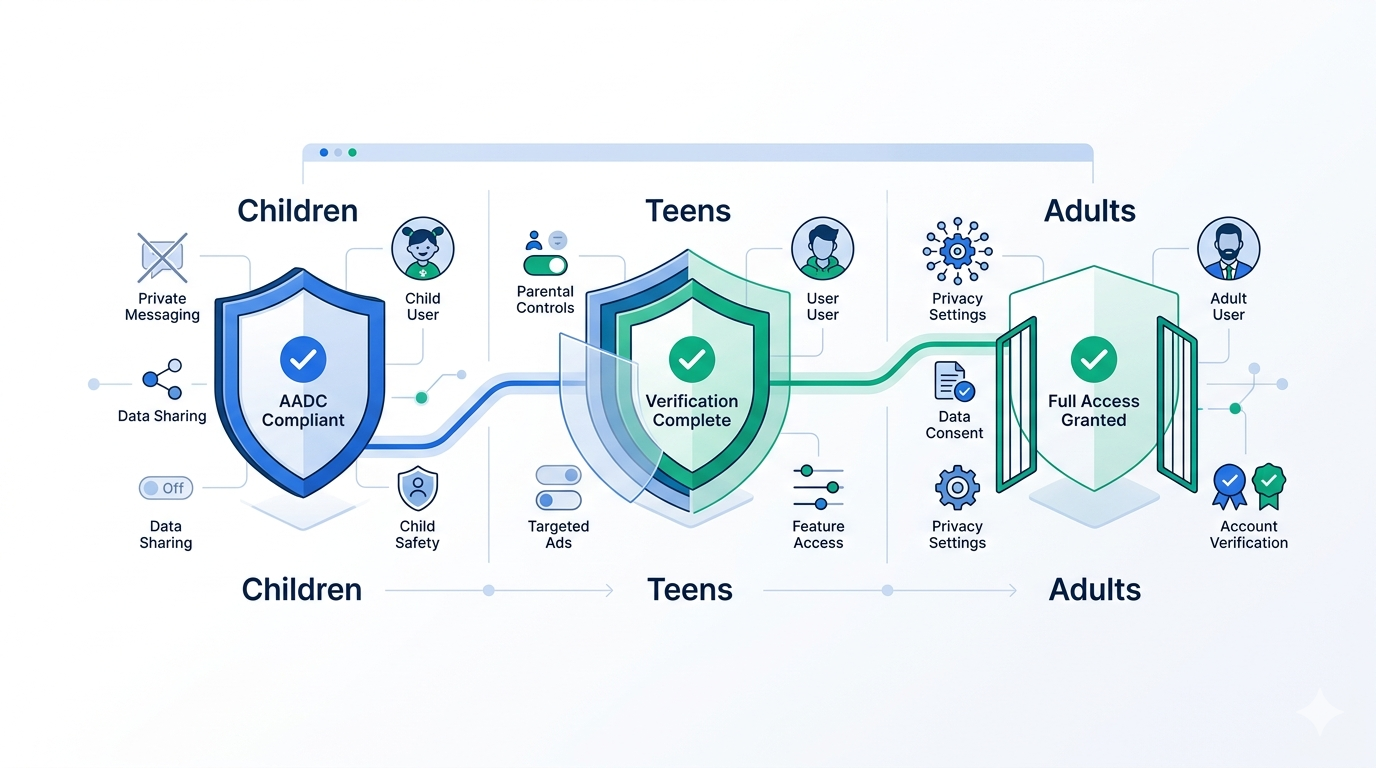
Age collection at account creation. Every user must provide their date of birth to create an operating system account. This applies at the OS level — during device setup or account provisioning — not at the app level. Think the moment you configure a new iPhone, set up a Windows account, or create a user profile on a Chromebook.
Parental verification for minors. If the declared age is under 18, a parent or legal guardian must verify the minor’s age. The bill doesn’t specify which verification method parents must use — that’s punted to FTC rulemaking within 180 days of enactment. But the intent is clear: self-declaration by a minor alone is not sufficient.
Age signal API for developers. OS providers must build systems through which app developers can access age-verification information. This is the most consequential provision for anyone building apps. Instead of each developer independently solving age verification, the OS would provide a standardized signal — and developers would be expected to consume it.
FTC enforcement. The FTC would be responsible for establishing regulations covering shared devices, parent verification methods, and data protection standards. Compliant providers get a safe harbor — they can’t be held liable under the act.
Timeline. The bill would take effect one year after enactment. The FTC has 180 days post-enactment to establish implementing regulations, and must submit a compliance report to Congress within 18 months.
How This Differs from State Laws
If you’ve been tracking state-level age verification legislation — and if you’re reading this blog, you probably have — you might be wondering what’s new here. After all, California’s AB 1043 already requires OS-level age bracketing (effective January 2027), and Colorado’s SB26-051 mandates device-level age verification.
The differences matter:
Federal preemption potential. State laws create a compliance patchwork. California wants four age brackets. Colorado mandates device-level verification but with different technical requirements. Texas and Louisiana focus on app store gatekeeping. A federal standard could — depending on the final text — preempt this fragmentation. For developers operating nationally, one standard beats fifty.
Mandatory parental involvement. Most state laws focus on collecting and sharing age signals. H.R. 8250 goes further by requiring active parental verification for minor accounts. This is a consent mechanism, not just a data collection requirement. It pushes the architecture closer to the verified parental consent (VPC) frameworks we’ve seen under COPPA — but applied universally at the OS level.
Developer access mandate. California’s AB 1043 requires OS providers to collect age data and share it with apps. H.R. 8250 takes the same approach but at the federal level, creating a potential nationwide API standard. If this becomes law, every app developer in the US would have access to an OS-provided age signal — regardless of which state their users are in.
Broader OS definition questions. The bill’s title refers to “operating system providers,” but the text (once available) will need to define this precisely. Does it cover only Apple, Google, and Microsoft? What about Linux distributions? Gaming consoles? Smart TV platforms? The scope question is critical and currently unanswered. The Linux community is already raising concerns — System76 published a public response, and Fedora’s community forums are debating architectural compliance approaches.
What Developers Should Actually Prepare For
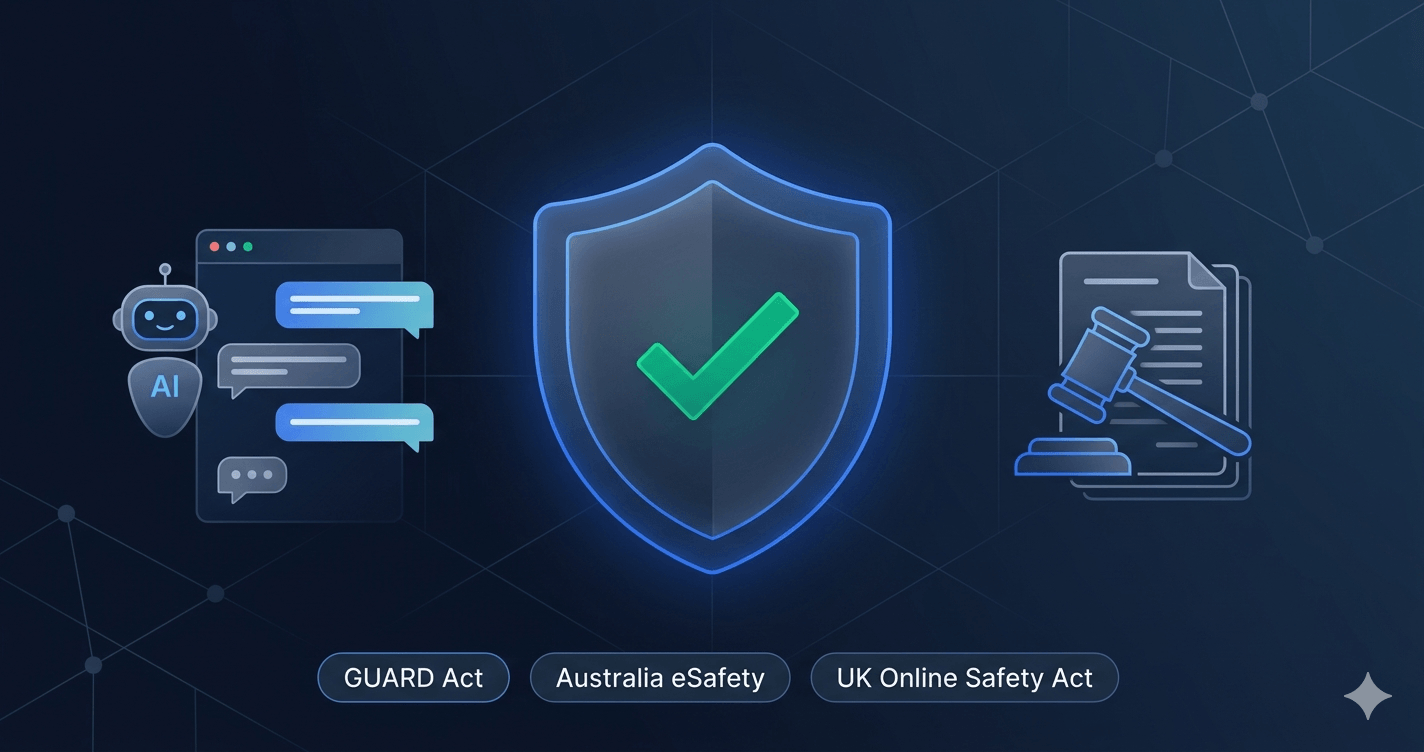
Let’s be direct: H.R. 8250 is an early-stage proposal. It’s been referred to the House Committee on Energy and Commerce, and it may change substantially, stall in committee, or never reach a floor vote. But the trajectory is unmistakable. Between state laws already in effect, the KIDS Act advancing through committee, and now a federal OS-level mandate, the direction of regulation is clear.
Here’s what’s worth doing now — regardless of whether this specific bill passes.
1. Architect for OS Signal Consumption
If you’re building a consumer-facing app, your verification stack should already be capable of consuming OS-level age signals. Apple’s Declared Age Range API is live. Google’s Play Age Signals API is approaching GA. Even if H.R. 8250 never becomes law, these APIs exist and will increasingly be expected by regulators and platform review processes.
The integration pattern is straightforward: query the OS-level API at app launch or account creation, receive a categorical age signal (not a birthdate), and use it as your first-pass verification. If you’re not already doing this, start now — the integration cost is low, and it reduces friction for the majority of your users.
2. Build a Fallback Stack
OS-level signals solve part of the problem. They don’t solve all of it:
- Web platforms don’t have access to OS-level APIs. If you have a web app, you need application-level verification.
- Self-declared age data at the OS level can be inaccurate. A 14-year-old who lied about their age during device setup will produce a “18+” signal that’s technically valid but factually wrong.
- Shared devices complicate the signal. A family iPad configured with a parent’s Apple ID will tell your app every user is an adult.
- High-assurance jurisdictions (UK Ofcom, Germany KJM, France ARCOM) require verification methods that go beyond self-declaration — even if that self-declaration happens at the OS level.
Your fallback should include AI-powered age estimation for medium-assurance scenarios and full document verification with liveness detection for high-assurance contexts. This layered approach is what regulators are actually looking for.
3. Implement Verified Parental Consent Flows
H.R. 8250 requires parental verification for minor accounts. Even if this bill doesn’t pass, the regulatory trend toward verified parental consent is accelerating — COPPA’s amended rules (effective April 22, 2026) already require enhanced consent mechanisms, and multiple state laws are moving in the same direction.
If your app has users under 18 — or if it should but currently doesn’t know — you need a VPC flow. The FTC’s February 2026 policy statement explicitly encouraged platforms to implement age verification as a prerequisite for COPPA compliance, and signaled enforcement flexibility for platforms that do so in good faith.
4. Monitor the Definition of “Operating System Provider”
This is the wildcard. If the bill defines “operating system provider” narrowly (Apple, Google, Microsoft), the compliance burden falls on three companies, and developers simply consume their APIs. If the definition is broad enough to capture gaming platforms, smart TV OSes, or embedded systems, the landscape gets more complex — and the API standardization benefits diminish.
Watch the committee markup. The definition will shape everything downstream.
5. Don’t Bet on a Single Signal Source
The worst architectural decision you can make right now is building your entire compliance strategy around a single verification method — whether that’s OS-level signals, document checks, or age estimation. Regulations vary by jurisdiction, enforcement standards differ, and the technical landscape is evolving quickly.
Build a verification orchestration layer that can route users to the appropriate method based on context: jurisdiction, content risk level, device type, and signal availability. This is the architecture that survives regulatory change without requiring a rewrite.
The Privacy Tension
H.R. 8250 raises the same privacy concerns that have followed every age verification mandate. The Electronic Frontier Foundation warned that OS-level requirements “expand the collection of sensitive age data” and increase “privacy and censorship risks.” Proton published an analysis noting that OS-level verification effectively makes Apple and Google “gatekeepers of age signals used across millions of apps” — concentrating identity infrastructure in two companies.
These concerns are legitimate. Age verification at the OS level creates a persistent identity layer that didn’t previously exist at the device level. If a device knows a user is 14, that signal flows to every app — not just age-restricted ones. The potential for over-restriction, profiling, and data breach exposure is real.
This is precisely why privacy-preserving verification matters. The right architecture doesn’t require exposing a user’s exact age, identity documents, or biometric data to every app on their device. It produces a categorical signal — “meets age threshold” or “does not” — and nothing more. Zero-knowledge approaches, on-device processing, and token-based returning-user flows are all techniques that satisfy the regulatory intent without creating a surveillance layer.
Where This Leaves Platform Operators
The regulatory direction is clear, even if the exact timeline isn’t. Whether H.R. 8250 passes as written, gets amended, or serves as a template for a future bill, the expectation that OS providers will build age verification infrastructure — and that app developers will consume it — is becoming the baseline assumption in Washington.
For platform operators, the actionable takeaway is the same one we’ve been advocating: build a layered verification architecture that can adapt to changing regulatory requirements without fundamental rearchitecture. Consume OS signals where available. Implement application-level verification where they’re not. Use privacy-preserving methods throughout. And measure the conversion impact at every tier.
The platforms that treat age verification as a one-time compliance checkbox will be rebuilding their stack every time a new law passes. The platforms that build flexible, layered verification infrastructure will adapt and move on.
How Xident Helps
Xident is designed for exactly this regulatory environment — one where the verification requirements vary by jurisdiction, device, and risk level, and where the rules are still being written.
Our platform provides:
- OS signal ingestion — consume Apple Declared Age Range and Google Play Age Signals as a first-pass check, with automatic fallback when signals are unavailable or insufficient
- AI-powered age estimation — on-device facial age analysis for medium-assurance scenarios, keeping biometric data client-side
- Document verification with liveness detection — full identity document verification for high-assurance jurisdictions (KJM, ARCOM, Ofcom)
- Verified parental consent flows — built-in VPC mechanisms that satisfy COPPA’s amended rules and state-level parental consent requirements
- Xident ID tokens — privacy-preserving returning-user credentials that eliminate re-verification friction
- Configurable flow orchestration — define escalation rules based on jurisdiction, device type, risk level, and signal confidence
Whether H.R. 8250 passes next month or next year, your verification stack should be ready. Talk to our team or explore the docs to get started.
Want to understand how OS-level signals fit into a layered verification strategy? Read our deep dive on Device-Level Age Verification from Apple and Google or our guide to Verified Parental Consent implementation.