Age verification was the compliance story of 2025. Verifiable parental consent (VPC) is the compliance story of 2026.
On April 2, Idaho Governor Brad Little signed HB 542 into law, requiring social media platforms to verify the age of every Idaho user and obtain verifiable parental consent for anyone under 16. On July 1, Nebraska’s LB 383 takes effect with similar obligations for under-18 users. And on April 22 — seven days from now — the FTC’s amended COPPA Rule codifies new approved VPC methods that every operator serving under-13 users must support.
For platform engineers and compliance teams, this creates a specific problem. Age verification answers “how old is this user?” Parental consent answers a harder question: “is this specific adult the legal guardian of this specific minor, and have they actually authorized what we’re about to do?” The two flows share infrastructure, but they are not interchangeable, and the laws increasingly treat them as distinct obligations with different evidentiary burdens.
This post breaks down what the 2026 VPC landscape actually requires, which consent methods are defensible under which laws, and how to architect a flow that doesn’t force your product team to choose between compliance and conversion.
Why VPC Is Different From Age Verification
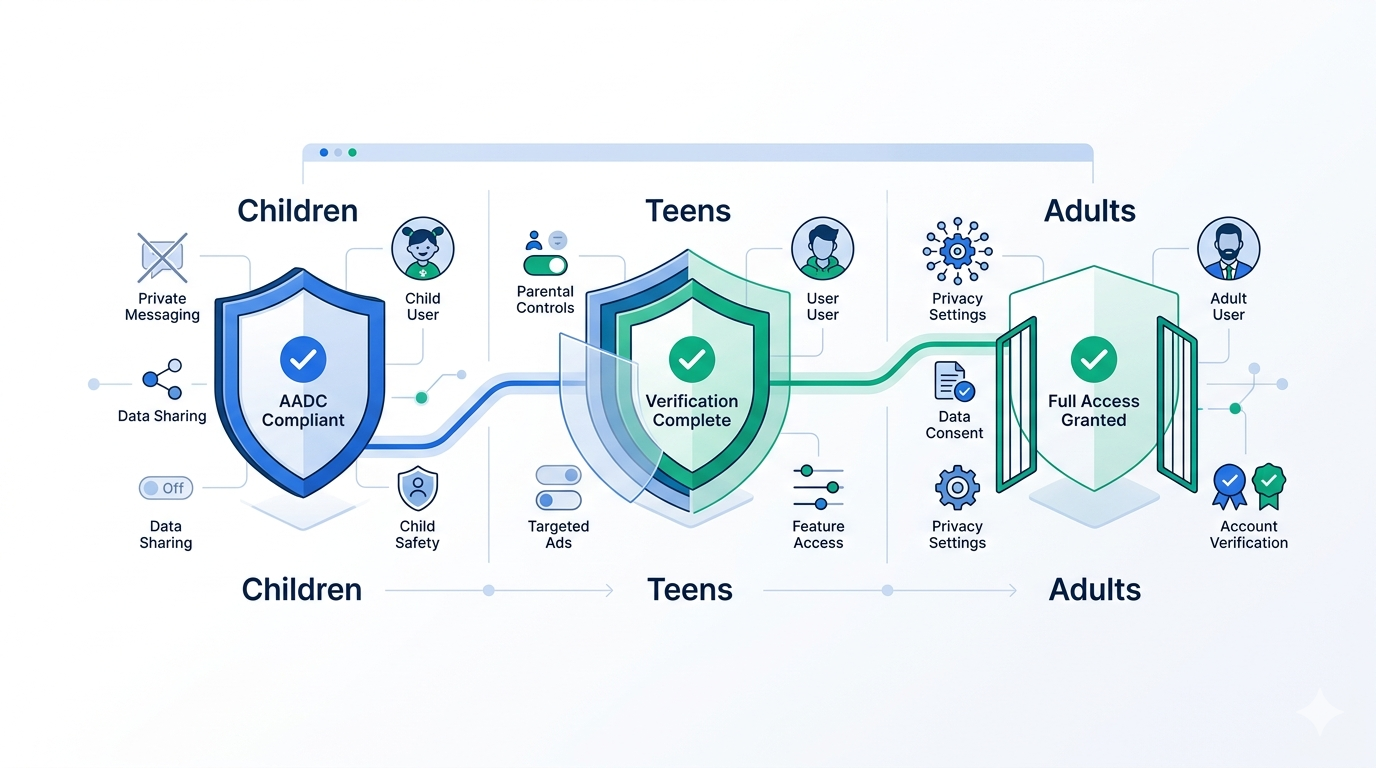
Age verification establishes a single fact about a single person: they are (or are not) above a threshold. It answers a binary question and, done well, produces an auditable record tied to that user’s session.
VPC requires establishing three additional facts:
- The person granting consent is an adult (typically the parent or legal guardian).
- That adult has a recognized legal relationship to the specific minor.
- The adult has affirmatively authorized specific data collection, account creation, or service use.
Each fact has its own verification problem. The first is standard age verification. The second is identity linkage — the hardest part — because “parent of minor X” is not something you can read off a government ID. The third is consent logging, which must be durable, tamper-evident, and tied to specific disclosures that were actually presented to the parent at the moment of consent.
Treat these as three orthogonal requirements, not one flow. Operators that collapse them into a single step — “click here to confirm you’re a parent” — are the operators the FTC has historically enforced against.
The 2026 Regulatory Stack
COPPA Amended Rule (effective April 22, 2026)
The FTC’s amended COPPA Rule doesn’t just tighten data handling; it expands the menu of approved VPC methods. Operators collecting personal information from under-13 users must use one of the enumerated methods. The new additions matter because they are the first methods to acknowledge that signed paper forms and credit-card micro-charges are not the future of consent.
Approved methods under the amended rule include:
- Signed consent form (physical or electronic signature) returned by mail, fax, or electronic scan.
- Credit card, debit card, or other online payment system that provides notification of each discrete transaction to the primary account holder.
- Call to a toll-free number staffed by trained personnel.
- Video conference with trained personnel.
- Government-issued ID verification, with the ID checked against databases and deleted promptly.
- Knowledge-based authentication (KBA) — newly codified, using dynamic, out-of-wallet questions.
- Government ID plus facial recognition matching — newly codified, where a selfie is matched against the photo on the submitted ID.
- SMS-based consent — newly approved in limited circumstances.
The “collect personal information internally only” pathway (formerly called “email plus”) remains available but continues to carry higher litigation risk because it does not actually verify the adult’s identity.
Idaho HB 542 (effective January 1, 2027, but implementation planning starts now)
Idaho’s Stop Addictive Social Media Act applies to social media platforms with Idaho users under 16. The law requires:
- Age verification for all Idaho users at account creation.
- Verifiable parental consent before account creation for users under 16.
- Parental access controls including the ability to revoke consent and delete the account.
- Restrictions on default notification settings and algorithmic feed delivery for minor accounts.
Importantly, HB 542 does not enumerate approved VPC methods with COPPA’s specificity. It requires “commercially reasonable” verification — a standard that courts and the Idaho Attorney General will interpret, and one that in practice tracks the COPPA method list closely.
Nebraska LB 383 (effective July 1, 2026)
Nebraska’s Parental Rights in Social Media Act goes further than Idaho by applying to users under 18, not 16. Platforms must:
- Verify age of every user.
- Obtain verifiable parental consent for minors before account creation.
- Provide parents with oversight tools including view access, time limits, and account termination.
- Retain consent records in a form that can be produced on request to the Attorney General.
The July 1 deadline is the most aggressive in the current wave. If you serve Nebraska users and haven’t started VPC implementation, you are already behind.
California SB 976 (age assurance standards expected late 2026)
California’s Protecting Our Kids from Social Media Addiction Act delegates specific method standards to the Attorney General, who held a public hearing in November 2025. Final standards are expected in the second half of 2026 with a compliance date at year-end. The hearing record signals a strong preference for privacy-preserving methods and skepticism of open-ended government-ID collection.
The VPC Method Decision Matrix
Not every method is appropriate for every use case. The right choice depends on the regulatory stack you’re subject to, your user base, your fraud tolerance, and your conversion economics.
Knowledge-Based Authentication (KBA)
How it works: The parent answers dynamic, out-of-wallet questions generated from public records and credit bureau data (prior addresses, vehicle registrations, loan amounts). Correct answers above a threshold return a verified result.
Strengths: Fast, no hardware required, no document collection. Works well for US adults with credit footprints.
Weaknesses: Brittle for adults without US credit history (immigrants, young parents, low-income populations). Growing fraud risk as data breaches leak the underlying answers. Does not cryptographically bind the parent to the child.
Use when: US-only product, adult parents with established credit, moderate fraud tolerance.
Government ID Plus Facial Match
How it works: Parent submits a photo of a government-issued ID. A selfie is captured and matched against the ID photo using biometric comparison. Liveness detection prevents spoofing.
Strengths: Strong identity assurance. Works globally. Accommodates parents without US credit history.
Weaknesses: Higher friction than KBA. Creates a biometric collection point that is itself in scope under the amended COPPA Rule, state biometric privacy laws (BIPA, Texas CUBI), and GDPR Article 9 where applicable. Requires careful data minimization to stay defensible.
Use when: Global product, high fraud sensitivity, or when stronger identity assurance is needed for elevated-risk scenarios.
Video Conference with Trained Personnel
How it works: A live agent reviews the parent’s ID on camera, confirms the parent’s relationship to the child verbally, and logs consent.
Strengths: Highest assurance, accommodates edge cases (lost IDs, guardianship documents, translation needs). Regulators explicitly favor it.
Weaknesses: Enormous cost per verification. Impossible to scale for free or low-margin products. Staffing and training costs dominate the economics.
Use when: High-value accounts, enterprise products, remediation flows after a failed automated verification.
Signed Consent Form
How it works: Parent downloads a form, signs it (wet signature or e-signature meeting ESIGN/eIDAS standards), and returns it via email, upload, fax, or mail.
Strengths: Legally robust. E-signatures with audit trails create strong evidentiary records.
Weaknesses: Highest drop-off in conversion funnels. Unless the user is strongly motivated, expect significant abandonment.
Use when: Regulated contexts where strong documentary evidence matters more than conversion, or as a fallback from automated methods.
Credit Card Transaction
How it works: Parent authorizes a small transaction (commonly $0.50–$1.00) on a card that requires confirmation of the account holder’s adult status. The notification requirement distinguishes this from routine card authorization.
Strengths: Fast, familiar, integrates cleanly with existing payment infrastructure.
Weaknesses: Does not actually verify identity, only card possession. Card fraud remains a meaningful attack surface. Some regulators (notably California in SB 976 hearings) are skeptical. Not suitable for operators who do not otherwise need to charge the user.
Use when: Paid product where billing already happens, or a soft confirmation layer on top of another primary method.
SMS-Based Consent
How it works: Parent receives an SMS with a consent disclosure and confirms via reply. The FTC approved this in limited circumstances under the amended rule.
Strengths: Lowest friction, highest conversion. Works globally with minimal integration.
Weaknesses: The weakest identity assurance of any approved method. Only defensible when paired with prior age and identity verification of the phone number’s owner. The amended COPPA Rule constrains its standalone use.
Use when: As a confirmation step, not a primary method. Paired with number-owner verification and a clear consent disclosure.
A Reference VPC Architecture
Here is a consent flow pattern that satisfies the COPPA amended rule, Idaho HB 542, Nebraska LB 383, and is forward-compatible with California SB 976’s expected standards.
Step 1: Establish the minor. At account creation, run age estimation or age verification on the prospective user. If the user is flagged as likely a minor under the applicable threshold (13 for COPPA, 16 for Idaho, 18 for Nebraska), halt account provisioning and branch into the VPC flow.
Step 2: Establish the parent. Prompt the minor to provide a parent’s contact information (email and phone). Send a consent request to the parent with a unique token-bound URL. Do not provision the account yet; the minor’s session is in limbo until the parent completes the flow.
Step 3: Verify the parent as an adult. When the parent opens the consent link, run a VPC method appropriate to the risk profile. For most products, start with KBA or government ID plus facial match. Build in a fallback to video conference for users who fail automated methods.
Step 4: Establish the parent-minor link. This is the step most implementations skip. Require the parent to affirm, with a logged and timestamped action, the specific minor they are consenting for (by name and, where appropriate, date of birth). Optionally collect a relationship document (birth certificate, adoption decree, guardianship order) for higher-assurance contexts.
Step 5: Present disclosures and capture consent. Render the specific data collection, processing, and sharing disclosures in plain language. Capture consent with a timestamped action — not a pre-checked box. Log the hash of the disclosure text that was presented so you can prove what the parent actually saw.
Step 6: Produce a durable consent record. Generate a tamper-evident consent artifact: parent identity reference (not PII), minor reference, disclosure hash, consent timestamp, method used, verification evidence references. Store it in an append-only log with cryptographic integrity. This is what you produce when the Attorney General asks.
Step 7: Provision the account with parental controls. Only after consent is logged, provision the minor’s account with required parental oversight features: revocation flow, view access, time-limit controls, deletion.
The Data Minimization Imperative
Every VPC method creates collection obligations. The amended COPPA Rule’s retention limits, the state biometric privacy regimes, and GDPR all penalize operators who collect more than necessary.
The compliance-native pattern is to verify, prove, and discard:
- Process government ID and biometric data on-device where possible. Extract only the classification result (verified adult, verified match) and discard the underlying data.
- Where server-side processing is unavoidable, use ephemeral processing enclaves with strict deletion SLAs (minutes, not days). Log the deletion.
- Store consent artifacts, not consent evidence. The artifact is a cryptographic proof that a method was used and succeeded. The raw evidence (ID images, biometric templates, KBA answers) should be deleted once the artifact is produced.
- Use reusable verified credentials where the jurisdiction allows. A parent who verified once should not need to re-verify for every minor they manage or every product they consent to.
This is the architecture that turns COPPA’s retention limits from a compliance cost into a competitive advantage: there is nothing on your servers to retain, breach, or disclose.
What to Build Before July 1
If you serve US minors and don’t yet have a defensible VPC flow, the practical priority list is:
- Inventory your minor-facing surfaces. Any flow that could be entered by an under-18 user is in scope for at least one 2026 law. Identify them.
- Pick a primary VPC method. For most consumer products, KBA or government ID plus facial match is the right starting point. Build both; A/B test for conversion.
- Build the parent-minor linkage step. This is where most implementations fail. Make the affirmation explicit, logged, and tied to the specific minor.
- Build a durable consent artifact store. Append-only, cryptographically verifiable, queryable by regulator subpoena.
- Build the revocation flow. Every 2026 law requires parents to be able to revoke consent and delete the account. Design this up-front, not as a post-launch add-on.
- Test against the disclosures. Present the actual disclosure text you’ll use to parents. If it takes three paragraphs to explain what you’re collecting, it’s time to reduce what you collect.
- Document your method selection. Write down why you chose the methods you chose, what you rejected, and your fallback chain. This documentation is what protects you when the AG’s office asks.
Where Xident Fits
Xident provides the verification primitives that sit under a VPC flow: age verification, identity verification, document verification, biometric matching, and a reusable credential layer that lets parents verify once and grant consent across products without re-submitting PII.
Our architecture processes biometric data on-device and produces verifiable credentials that carry the consent evidence without carrying the underlying data. For operators navigating Idaho HB 542, Nebraska LB 383, and the COPPA amended rule, that means a single integration that covers the core verification requirements of every current US regime, with a privacy posture that minimizes the data you hold and the obligations that come with it.
The July 1 deadline is 76 days away. If you’re serving US minors and VPC isn’t on your engineering roadmap yet, it needs to be this sprint.
If you’d like to see how Xident’s VPC building blocks fit your stack, contact us — we can walk through your specific state coverage and method selection.