A quiet but consequential shift is underway. Age verification — historically implemented at the application layer through document uploads, selfie checks, or self-declaration checkboxes — is moving into the operating system itself. Apple and Google are building age signals directly into iOS and Android, and a wave of state legislation is making it mandatory.
This isn’t a theoretical future. Apple’s Declared Age Range API is live. Google’s Play Age Signals API is in beta. Colorado, California, Texas, and Louisiana already have laws on the books requiring device-level or app-store-level age checks. The KIDS Act, which incorporates KOSA, advanced out of the House Energy and Commerce subcommittee in March 2026.
For platform operators, this changes the compliance calculus fundamentally. Here’s what you need to understand.
The Architecture: How OS-Level Age Signals Work
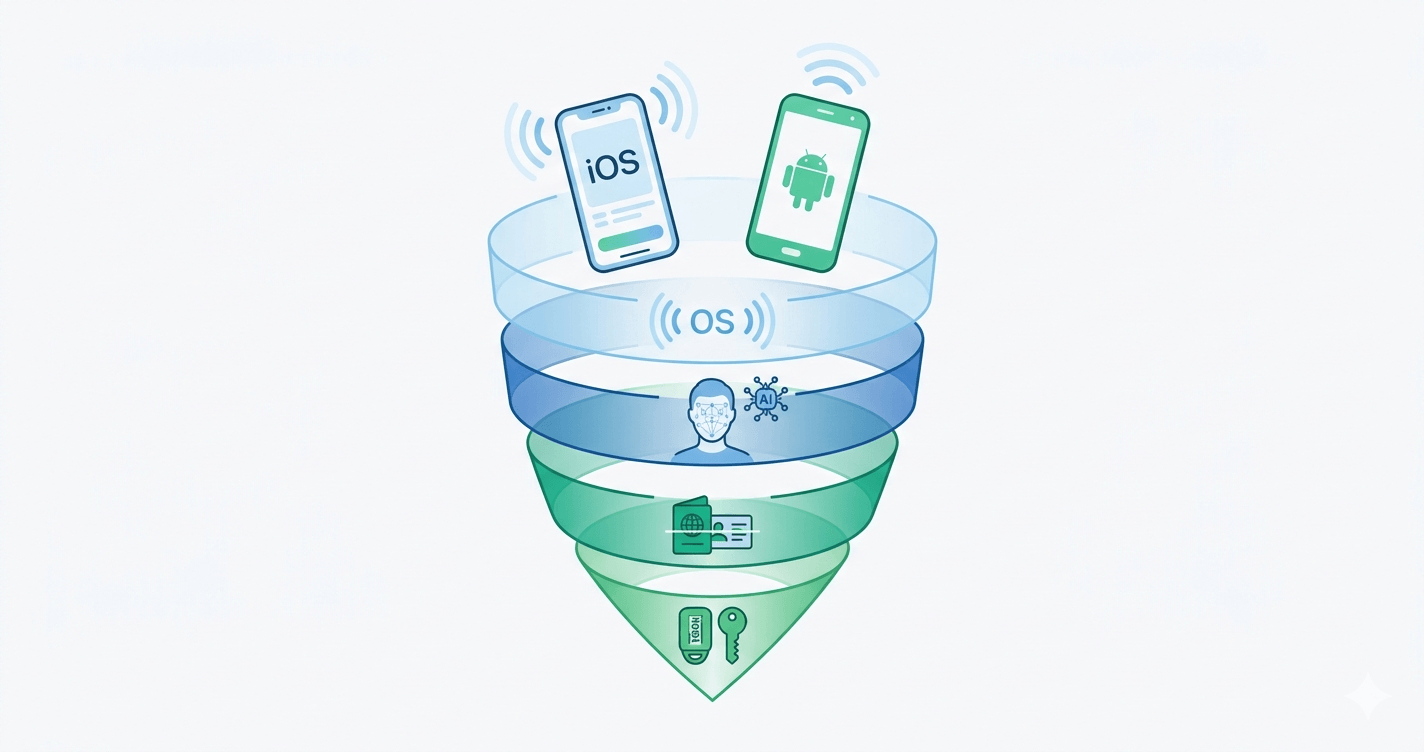
Device-level age verification introduces a new layer in the verification stack. Instead of each application independently verifying a user’s age, the operating system provides a privacy-preserving signal that applications can consume.
Apple’s Declared Age Range API returns a coarse age bracket — not an exact birthdate. When a user sets up an Apple device or configures Family Sharing, Apple captures age information. Apps can then query the API to receive a signal like “this user is in the 18+ range” without ever seeing the underlying data. The biometric or credential check stays entirely within Apple’s ecosystem.
Google’s Play Age Signals API follows a similar model. Currently in beta, it allows Android apps to request age-range signals from Google Play. The signal is derived from the user’s Google account configuration, parental controls, and Play Store settings.
The privacy model is significant: neither API exposes personally identifiable information to the requesting application. The app gets a boolean or categorical answer — “meets age threshold” or “does not meet age threshold” — and nothing more.
The Legislative Push
This isn’t just a platform initiative. Legislation is driving adoption:
California AB 1043 (signed October 2025) requires device manufacturers — specifically Apple and Google — to collect age or date of birth during device setup. This makes the OS-level signal more reliable by ensuring the underlying data exists.
Colorado SB26-051 goes further, requiring OS providers to verify user age at the device level. This is the most comprehensive device-level mandate in the US, effectively making Apple and Google the first gatekeepers in the age verification chain.
Texas and Louisiana app store accountability laws took effect January 1, 2026, requiring app stores to verify users are at least 18 before downloading age-restricted apps.
The federal KIDS Act (incorporating KOSA) would mandate age verification for accessing mature content and require platforms to implement rigorous controls for minor accounts. It advanced through subcommittee in March 2026.
The trajectory is clear: device-level signals are becoming a regulatory expectation, not just a convenience.
Why OS-Level Signals Alone Aren’t Enough
Here’s where the industry conversation gets nuanced — and where platform operators need to think carefully.
A March 2026 analysis from Biometric Update titled “The OS-Level Mirage” made the case plainly: Apple and Google can’t solve the age assurance crisis alone. There are several structural reasons:
Coverage gaps. Not every user has a properly configured Apple or Google account. Shared devices, enterprise devices, sideloaded apps on Android, and web-based platforms all fall outside the OS-level signal’s reach. If your product is web-first or supports non-mobile access, OS signals cover only a fraction of your user base.
Signal confidence. The age data in these APIs is self-declared during account setup. A 14-year-old who entered a false birthdate when creating a Google account will produce a “18+” signal that’s technically correct according to the API but factually wrong. Regulators — particularly the UK’s Ofcom and ICO — have made clear that self-declaration is insufficient for “highly effective” age assurance.
Jurisdictional mismatch. Different regulators have different standards. Germany’s KJM requires specific technical measures. France’s ARCOM demands double anonymity. The UK’s Online Safety Act requires age assurance that is “highly effective.” A coarse OS-level signal may satisfy a Texas app store law but fail to meet European standards.
Web platform blind spot. Device-level APIs are designed for native apps. If your platform operates primarily through a web browser — as many e-commerce, gaming, and content platforms do — OS-level signals aren’t available at all.
The Layered Verification Model
The practical answer isn’t choosing between OS-level signals and application-level verification. It’s layering them.
A well-architected age verification strategy in 2026 looks like this:
Layer 1 — OS-level signals (where available). Consume Apple’s Declared Age Range API or Google’s Play Age Signals as a first-pass check. If the signal confirms the user meets the age threshold, and your regulatory requirements accept this level of assurance, you can proceed with minimal friction. This keeps your conversion funnel intact for the majority of users.
Layer 2 — AI-powered age estimation. For users where OS signals are unavailable, inconclusive, or insufficient for your regulatory context, escalate to biometric age estimation. On-device facial analysis can estimate age within seconds, without requiring document uploads. This is the sweet spot between friction and confidence.
Layer 3 — Document verification. For high-risk transactions, regulatory regimes that demand it (like KJM or ARCOM), or cases where age estimation confidence is low, escalate to full document verification with liveness detection. This is the highest-assurance tier.
Layer 4 — Token-based returning users. Once a user has been verified at any layer, issue a privacy-preserving token (like an Xident ID) so they don’t need to re-verify on subsequent visits. This is where the real conversion optimization happens — verified users pass through instantly.
The key insight: matching the verification method to the risk level is how you stay compliant without destroying your conversion rate. Research shows that platforms implementing aggressive, one-size-fits-all verification see conversion drops of up to 40%. A tiered approach minimizes friction for low-risk scenarios while maintaining full assurance where it matters.
What This Means for Platform Operators
If you’re building or operating a platform that will need age verification — and in 2026, that’s most consumer-facing digital products — here’s the practical takeaway:
Start integrating OS-level signals now. Even if they’re not sufficient on their own, they reduce friction for a large segment of your users. Apple’s API is stable; Google’s is approaching GA. The integration cost is low relative to the UX benefit.
Don’t treat OS signals as complete compliance. No regulator we’re aware of has stated that consuming an Apple or Google age signal alone satisfies their requirements for high-risk content or services. You need a fallback stack.
Invest in tiered verification infrastructure. Build your verification flow so that the method escalates based on context: jurisdiction, content risk level, signal availability, and confidence score. This is the architecture that scales across regulatory regimes.
Measure conversion impact at each tier. Instrument your verification funnel the way you’d instrument any critical user flow. Know your drop-off rates at each verification step, and optimize accordingly.
Plan for web. If you have a web presence — and you almost certainly do — you need a verification strategy that works outside the app store ecosystem entirely.
Where Xident Fits
Xident is built for exactly this layered model. Our verification platform supports:
- OS signal consumption — ingest Apple Declared Age Range and Google Play Age Signals as first-pass checks
- On-device age estimation — AI-powered facial age analysis that runs client-side, keeping biometric data off your servers
- Document verification with liveness detection — for high-assurance scenarios requiring KJM, ARCOM, or Ofcom compliance
- Xident ID tokens — privacy-preserving returning-user tokens that eliminate re-verification friction
- Configurable verification flows — define escalation rules based on jurisdiction, risk level, and signal confidence
The result: you meet compliance requirements across jurisdictions while keeping friction proportional to risk. Your 18-year-old user in Texas with a properly configured iPhone breezes through. Your user accessing age-restricted content on a web browser in Germany gets the full verification stack. Both are compliant. Neither is over-verified.
The Bottom Line
Device-level age verification is a genuine improvement in the ecosystem — more privacy-preserving, lower friction, and backed by serious legislative momentum. But it’s a foundation layer, not a complete solution.
The platforms that will navigate 2026’s regulatory environment successfully are the ones building layered verification architectures: OS signals where available, biometric estimation where needed, document verification where required, and token-based re-verification everywhere.
The age verification stack is becoming as essential as the authentication stack. The question isn’t whether to implement it — that’s settled. The question is whether your architecture is sophisticated enough to handle the complexity.
Ready to implement layered age verification? Talk to our team or explore the docs to get started in under 5 minutes.