On May 6, 2026, Utah became the first US state to directly target the use of VPNs and proxy servers to bypass age verification requirements. Senate Bill 73, signed by Governor Spencer Cox on March 19, fundamentally changes the compliance calculus for any platform serving age-restricted content to US users.
The law’s core premise is simple: if a user is physically in Utah, they’re subject to Utah’s age verification requirements regardless of what their IP address says. But the technical and legal implications for platform operators are anything but simple.
What SB 73 Actually Says
Utah’s existing age verification statute already required platforms hosting material harmful to minors to verify users’ ages. SB 73 amends this framework with a critical addition: a user is deemed to be accessing a website from Utah if they are physically present in the state, regardless of whether they use a VPN, proxy server, or any other tool to mask their geographic location.
The law goes further than just establishing jurisdiction. It prohibits platforms from providing instructions on how to use a VPN to circumvent age checks — a provision that digital rights groups, including the Electronic Frontier Foundation, have flagged as a likely First Amendment violation.
For platforms, three things changed on May 6:
-
Jurisdiction follows the user, not the IP. You can no longer rely on IP-based geo-detection as your compliance boundary. A Utah user connecting through a server in Germany is still your liability.
-
Ignorance isn’t a defense, but detection isn’t mandatory. The law doesn’t require platforms to detect VPN usage or determine a user’s true location. But if you know or reasonably should know that a user is in Utah, you must verify their age.
-
Anti-circumvention speech restrictions. You cannot publish guides, FAQs, or support content explaining how to use VPNs to avoid your own age gates.
The Compliance Paradox
NordVPN has described SB 73 as creating an “unresolvable compliance paradox,” and they’re not wrong about the difficulty — though the paradox has practical solutions.
The problem as stated: if a platform can’t reliably detect whether a user is using a VPN, and the law holds them liable for VPN users’ true locations, what exactly should the platform do?
Platforms have responded (or are planning to respond) with one of four strategies:
Strategy 1: Geo-block Utah entirely. Several smaller adult content platforms have already taken this approach. It’s the simplest option but it abandons Utah-based customers entirely, and it’s easily circumvented — ironically, by the same VPNs the law targets. A user outside Utah can VPN into another state, and a Utah user can appear to be outside the state. Geo-blocking is a business decision, not a compliance solution.
Strategy 2: Block known VPN IP ranges. Some platforms maintain lists of IP addresses associated with commercial VPN services and block them. This is a cat-and-mouse game by definition. VPN providers rotate IPs constantly. Residential proxy services are nearly undetectable. And blocking VPN IPs penalizes every privacy-conscious user, not just minors attempting to circumvent age gates.
Strategy 3: Require age verification for all users globally. If you can’t reliably determine who’s in Utah, verify everyone. This eliminates the geographic detection problem entirely but introduces massive friction for your global user base and raises privacy concerns in jurisdictions where blanket verification isn’t required or may even violate data minimization principles.
Strategy 4: Implement identity-layer verification that makes circumvention irrelevant. This is where the industry is heading, and it’s the only approach that actually resolves the paradox.
Why Identity-Layer Verification Solves This
The VPN problem exists because current age verification approaches are tightly coupled to geography. The typical flow is: detect the user’s location via IP → determine which jurisdiction’s rules apply → trigger verification if required. VPNs break step one, which breaks everything downstream.
Identity-layer verification decouples age assurance from geographic detection. Instead of asking “where is this user?” and then “how old are they?”, you ask a single question: “has this user proven they meet the age threshold?”
Here’s what this looks like in practice:
Verification happens once, applies everywhere. A user verifies their age through a document check, biometric estimation, or credential presentation. That verification produces a cryptographic token — not a record of their identity, but a proof of their age status. The token travels with the user’s session regardless of their IP address, VPN usage, or geographic masking.
No geographic detection required. The platform doesn’t need to know where the user is. It needs to know whether the user has a valid age attestation. This sidesteps the entire VPN detection problem because the verification isn’t triggered by geography — it’s triggered by the attempt to access age-restricted content.
Privacy by design. Because the verification token proves age status without revealing identity, you’re not collecting location data, IP forensics, or VPN detection signals. You’re collecting the minimum data needed for compliance, which aligns with GDPR data minimization, CCPA requirements, and the privacy concerns that motivated VPN usage in the first place.
The Liability Signal for Other States
Utah is first, but it won’t be last. The pattern in US age verification legislation has been consistent: one state passes a novel provision, courts weigh in, and other states iterate on the model.
Several signals suggest anti-circumvention provisions will spread:
The UK is already moving. Following Ofcom’s age assurance guidance under the Online Safety Act, the UK government confirmed it may restrict children’s VPN usage to close enforcement loopholes. This isn’t legislation yet, but it’s in active consultation.
Denmark and Malaysia have both signaled intent to address VPN circumvention in their age verification frameworks during 2026.
The AVPA’s position paper on VPNs argues that circumvention is a “navigable challenge” for the age assurance sector, not a fundamental barrier — signaling that the industry’s own trade body doesn’t see VPNs as a reason to delay enforcement.
Other US states are watching the litigation. If SB 73 survives its inevitable constitutional challenges (particularly around the speech restrictions on VPN instructions), expect copycat provisions in the next legislative cycle.
For platform operators, the strategic implication is clear: building your compliance architecture around geographic detection is building on sand. Even if SB 73 gets struck down or narrowed, the regulatory direction is unmistakable — legislators want age verification to work regardless of the user’s technical sophistication.
What Platform Operators Should Do Now
If you’re operating a platform that serves age-restricted content or falls under child safety statutes, here’s a practical roadmap for dealing with the post-SB 73 landscape:
1. Audit Your Current Geographic Detection
Map out exactly how your platform determines user location and where that determination feeds into compliance logic. If your age verification trigger is “user IP resolves to a state with age verification requirements,” you have a single point of failure that VPNs exploit trivially.
2. Decouple Verification from Geography
Move toward a model where age verification is triggered by content access, not by geographic detection. This doesn’t mean verifying every user on every page load. It means that access to age-restricted content or features requires a valid age attestation, period, regardless of where the request originates.
3. Adopt Token-Based Returning User Flows
The biggest friction concern with universal age verification is requiring users to verify repeatedly. Token-based flows solve this: a user verifies once, receives a cryptographic age token, and presents that token on subsequent visits. The verification event is a one-time cost. The token is a zero-friction pass.
Xident’s returning user tokens work exactly this way. A user verifies through document check, biometric estimation, or an existing digital credential. On subsequent visits, the token confirms their age status without re-verification, without storing their identity, and without caring whether they’re connecting through a VPN, a coffee shop, or a Starlink terminal.
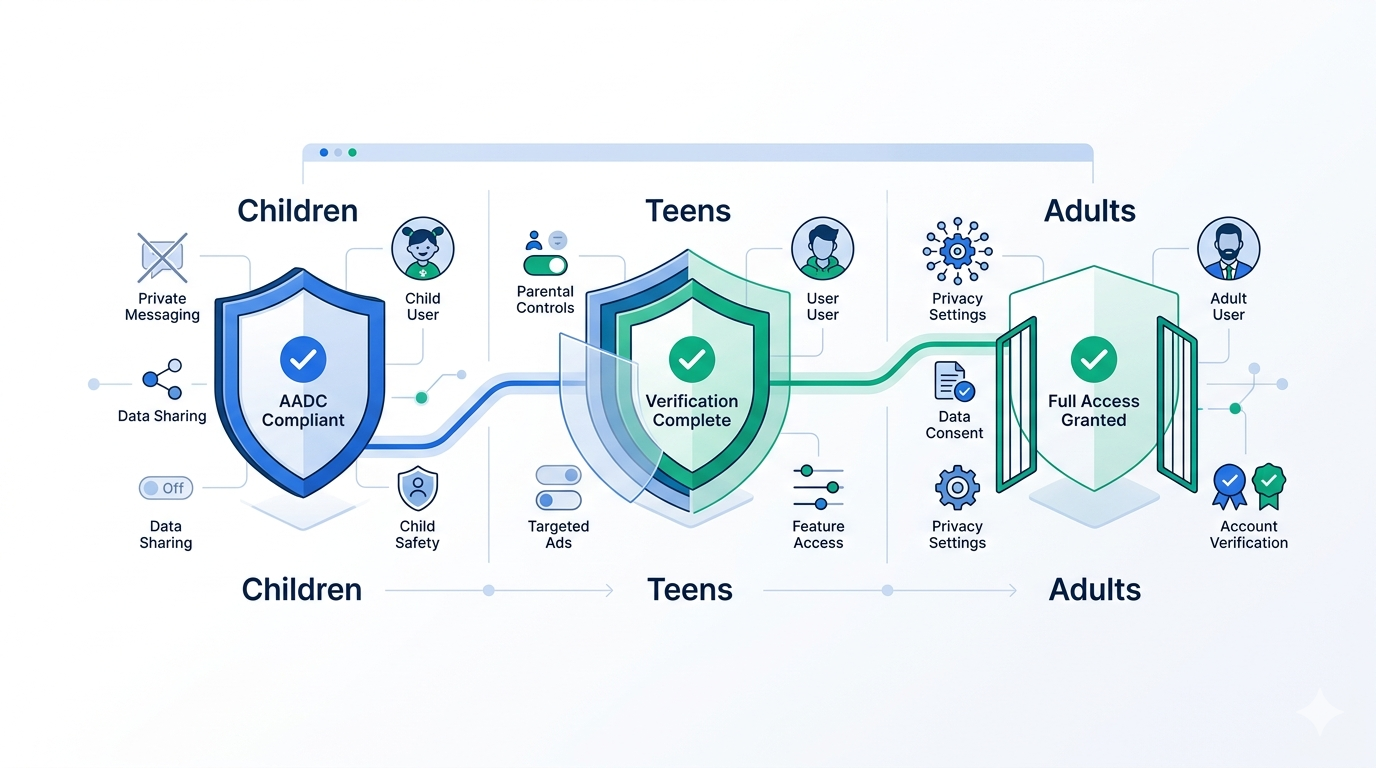
4. Prepare for Multi-Jurisdiction Compliance
SB 73 is one law in one state, but your compliance architecture needs to handle all of them. The platforms that will navigate this well are the ones building flexible verification flows that can adapt to different thresholds (13+, 16+, 18+, 21+), different evidence requirements (document, biometric, credential, parental consent), and different privacy regimes — without rebuilding their integration for each jurisdiction.
5. Review Your Support Content
SB 73’s prohibition on VPN circumvention instructions is novel and legally questionable, but until it’s challenged, audit your help documentation, FAQs, and support articles for anything that could be construed as instructing users on how to bypass your own age gates. This applies even to general privacy guides that mention VPN usage in the context of your platform.
The Bigger Picture: VPNs Aren’t the Problem
It’s worth stepping back from the compliance details to note what SB 73 actually reveals about the state of age verification.
The reason VPN circumvention is a legislative concern is that current age verification approaches are geographically brittle. They work by detecting where a user is and applying local rules. VPNs break geographic detection, so legislators are trying to make VPN usage itself the violation.
But this is treating the symptom, not the disease. The fundamental issue is that age verification has been bolted onto the network layer (IP geolocation) instead of being built into the identity layer (user attestations). When verification lives at the identity layer, VPNs are irrelevant. A user’s age status doesn’t change when they connect to a different server.
This is why the industry is converging on credential-based and token-based approaches — not because legislators demanded it, but because it’s the only architecture that works reliably in a world where users have (and should have) tools to protect their network privacy.
Utah’s SB 73 is a transitional law. It’s trying to hold together a geographic enforcement model that’s already breaking down. The platforms that build for what comes next — identity-layer verification that works regardless of network topology — won’t just comply with SB 73. They’ll be ready for whatever comes after it.
How Xident Handles This
Xident was designed from the ground up for exactly this scenario. Our verification architecture doesn’t depend on geographic detection, VPN blocking, or IP forensics.
Here’s how it works:
- User accesses age-restricted content → Your platform checks for a valid Xident age token
- No token exists → User goes through a verification flow (document check, biometric age estimation, or digital credential presentation — configurable per jurisdiction)
- Verification succeeds → Xident issues a cryptographic age token. No PII is stored. No identity record is created. Just a proof of age status.
- User returns (even via VPN) → The token is presented and validated. No re-verification needed. No geographic detection needed.
The entire flow is jurisdiction-aware but geography-independent. Whether the user is in Utah, the UK, or connecting through three layers of VPN, the age attestation is the same.
For platforms dealing with SB 73 and the wave of anti-circumvention provisions that will follow, this isn’t just a compliance advantage — it’s an architectural one. You stop playing whack-a-mole with VPN detection and start operating on a foundation that works regardless of how users connect.
Need to implement age verification that works regardless of VPNs, proxies, or geographic masking? Talk to our team or see how integration works in 5 minutes.