There’s a new kind of user hitting your platform. It doesn’t have a face. It doesn’t hold a passport. It can complete your entire sign-up flow in under 200 milliseconds — and your age verification system probably can’t tell it apart from a real person.
Welcome to the era of AI agents, where identity verification is no longer just about humans.
The Rise of Autonomous Agents
The shift from AI-as-assistant to AI-as-actor is accelerating faster than most compliance teams realize. Gartner predicts that 40% of enterprise applications will include integrated task-specific agents by the end of 2026 — up from less than 5% in 2025. These aren’t chatbots. They’re autonomous systems that browse the web, fill out forms, execute transactions, manage accounts, and interact with APIs on behalf of their operators.
In practical terms, this means AI agents are already doing things that trigger identity and age verification requirements: purchasing age-restricted products, accessing content behind age gates, signing up for services with minimum age requirements, and interacting with regulated platforms. The agent does it faster, at scale, and without the behavioral signals that traditional fraud detection relies on.
This creates a category of risk that most verification systems were never designed to handle.
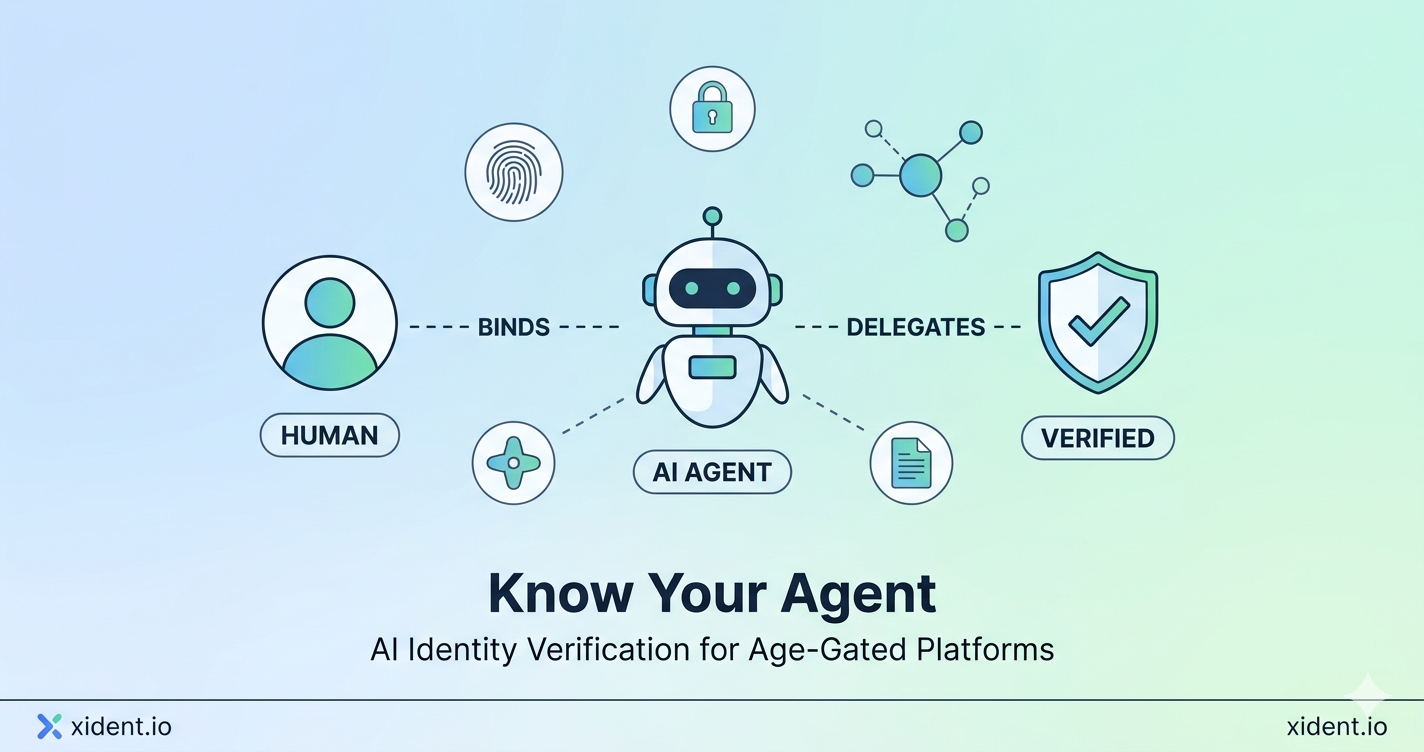
What Is Know Your Agent (KYA)?
Know Your Agent is the identity verification framework for autonomous AI systems — the conceptual equivalent of Know Your Customer (KYC) for non-human actors. The framework answers three questions that any platform receiving agent traffic needs resolved:
Identity. Who is this agent? What system created it, and what organization operates it? Without a reliable answer, you’re accepting traffic from an unknown source with unknown intent.
Authority. Is this agent authorized to perform the actions it’s attempting? An agent purchasing alcohol on behalf of a verified 30-year-old is fundamentally different from one operating without clear delegation. The distinction matters for compliance.
Accountability. If something goes wrong — a minor gains access through an agent, a fraudulent transaction occurs, a regulatory violation is triggered — who is responsible? KYA establishes the chain of accountability from agent to operator to human principal.
The framework is crystallizing rapidly. Sumsub launched its AI Agent Verification product in January 2026, binding agents to verified human identities through liveness checks and device intelligence. Blockchain-based approaches like ERC-8004 are creating on-chain trust scoring for agents transacting in DeFi. And enterprise platforms are building KYA into their API authentication layers.
This isn’t theoretical. It’s shipping.
Why Age-Gated Platforms Should Pay Attention Now
If you operate any platform with age restrictions — e-commerce selling alcohol or tobacco, online gambling, adult content, social media with minimum age requirements — you have a specific and urgent problem.
Your current verification flow was designed for humans. It assumes a person with a face, a document, and biological age. AI agents break every one of those assumptions.
Liveness detection doesn’t apply. An agent doesn’t have a face to check for liveness. If your verification relies on biometric age estimation or selfie-based liveness, an agent can potentially bypass or spoof these checks using generated media.
Document verification is trivially automated. An agent with access to document images can submit them at machine speed. Without additional signals, your system can’t distinguish between a person uploading their own passport and an agent uploading a document from a data breach.
Behavioral analytics lose signal. Traditional fraud detection looks for human behavioral patterns — typing speed, mouse movement, session duration. Agents produce synthetic behavioral signals that may look plausible but carry none of the reliability these systems depend on.
Volume amplification. A single agent can create hundreds of accounts across hundreds of platforms simultaneously. What was a one-at-a-time human fraud problem becomes a scaled automation problem.
The regulatory environment is tightening in parallel. The UK’s Online Safety Act enforcement now extends to user-generated content platforms. The EU Digital Services Act mandates age verification across member states. Half of US states have enacted age verification laws. None of these regulations distinguish between human and agent traffic — but all of them hold the platform accountable for failures.
If an AI agent bypasses your age gate and enables minor access to restricted content, the regulatory consequences fall on you, not on the agent’s operator.
The Verification Stack Needs a New Layer
The solution isn’t to abandon human verification — it’s to add a parallel verification path for non-human traffic. A modern verification architecture needs to handle both.
For human users, the flow remains familiar: document verification, biometric liveness, age estimation, and (ideally) a reusable credential like Xident’s Verify Once model that eliminates repeated verification through passkey authentication.
For agent traffic, you need a different set of checks:
Agent identification. Detect whether the incoming request originates from an agent. This involves analyzing request patterns, header signatures, behavioral fingerprints, and API-level metadata. The goal isn’t to block agents — it’s to classify them accurately.
Operator verification. Once an agent is identified, verify the human or organization behind it. This is where KYA meets KYC: the agent’s operator should have completed identity verification, and the agent should carry a cryptographic attestation binding it to that verified identity.
Delegation validation. Confirm that the agent is authorized to act on behalf of a specific verified user for a specific purpose. An agent purchasing wine for a verified 35-year-old should carry proof of that delegation — not just proof that its operator is a legitimate company.
Continuous monitoring. Unlike human sessions that have natural time boundaries, agents can maintain persistent connections and execute actions at scale. Monitoring agent behavior for anomalies — volume spikes, unusual access patterns, cross-platform coordination — becomes a continuous requirement.
How Xident Approaches Agent Verification
At Xident, we’ve been watching the agent verification space closely because it intersects directly with our core architecture.
Our Verify Once model already addresses the key challenge: establishing a verified identity once and issuing reusable credentials for subsequent access. This architecture extends naturally to agent scenarios.
When an agent acts on behalf of a Xident-verified user, the delegation can be validated against the user’s existing verified credential. The user has already completed document verification, biometric liveness, and age confirmation. The agent doesn’t need to repeat this — it needs to prove it’s authorized to act within the scope of that verified identity.
This approach has several advantages:
Privacy preservation. The agent never needs to transmit biometric data or identity documents. The verification already happened at the human layer. The agent carries a token, not a face.
Cost efficiency. Agent verification through delegation is dramatically cheaper than running full KYC on every agent interaction. For platforms processing thousands of agent-initiated requests, the difference is material.
Regulatory alignment. Regulators care about outcomes: was the person behind the transaction verified? Was the age gate effective? Delegation-based verification maintains the compliance chain without requiring the regulatory framework to define how agents themselves should be verified.
Scalability. A single verified human identity can authorize multiple agents for different purposes, each carrying scoped credentials. This matches how agents are actually deployed — one user might have a shopping agent, a content access agent, and a financial services agent, each with different authorization scopes.
What Compliance Teams Should Do Now
The agent verification landscape is evolving quickly, but the preparatory work is straightforward.
Audit your current detection capabilities. Can your verification system distinguish between human and agent traffic today? If you’re relying solely on CAPTCHA and basic bot detection, you’re already behind. Modern AI agents can solve CAPTCHAs and simulate human-like interaction patterns.
Classify your agent risk. Not all agent traffic is equal. An agent querying product information is low risk. An agent completing a purchase of age-restricted goods is high risk. Map your verification requirements to the actual risk each agent interaction presents.
Evaluate your API layer. If you offer APIs, you likely already have agent traffic. Review your API authentication to determine whether you can identify agents, validate their operators, and enforce authorization scopes.
Plan for delegation. The winning architecture will verify humans thoroughly and then extend that verification to their authorized agents. If your current system treats every interaction as an isolated verification event, you’ll struggle to accommodate agent-mediated access at reasonable cost.
Monitor regulatory signals. The EU’s AI Act, the UK’s Online Safety Act, and the US patchwork of state regulations are all converging on accountability requirements that will eventually address agent traffic explicitly. Being ahead of this curve is a competitive advantage.
The Verification Industry’s Next Inflection
The identity verification industry has spent the last decade optimizing for human users — faster document capture, better liveness detection, more accurate biometric matching. That work isn’t obsolete. It’s foundational.
But the next wave of growth will come from extending verified identity beyond the human session. AI agents, digital wallets, IoT devices, and autonomous systems all need identity, authorization, and accountability. The providers that build for this expanded surface will define the next era of trust infrastructure.
At Xident, we believe that Verify Once is the right primitive for this future. A single, privacy-preserving verification event that creates a reusable credential — one that humans authenticate with passkeys and agents validate through delegation. The same trust chain. The same compliance guarantee. Different access patterns.
The agents are already here. The question is whether your verification stack is ready for them.
Xident provides age and identity verification with sub-3-second completion and a 0.03% false pass rate. Our Verify Once architecture extends naturally to agent-mediated access. Start integrating today or contact our team to discuss agent verification for your platform.